The Agent Workflow
One diagram that explains the entire loop: from invoice intake through evidence retrieval, validation, approval, and execution with full audit logging.
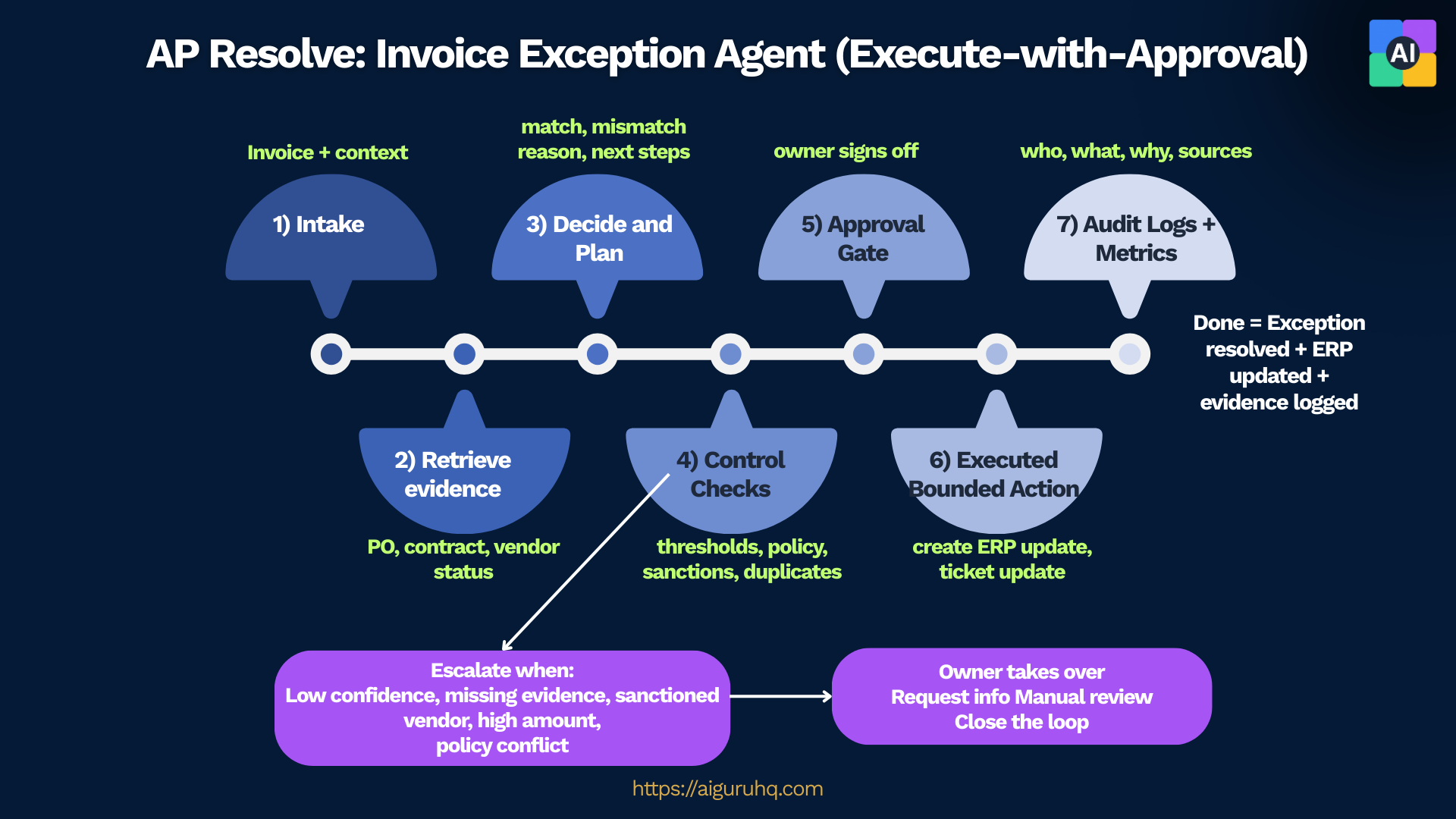
A reference implementation that shows how agentic workflows complete work safely using evidence, controls, and an audit trail.
One diagram that explains the entire loop: from invoice intake through evidence retrieval, validation, approval, and execution with full audit logging.
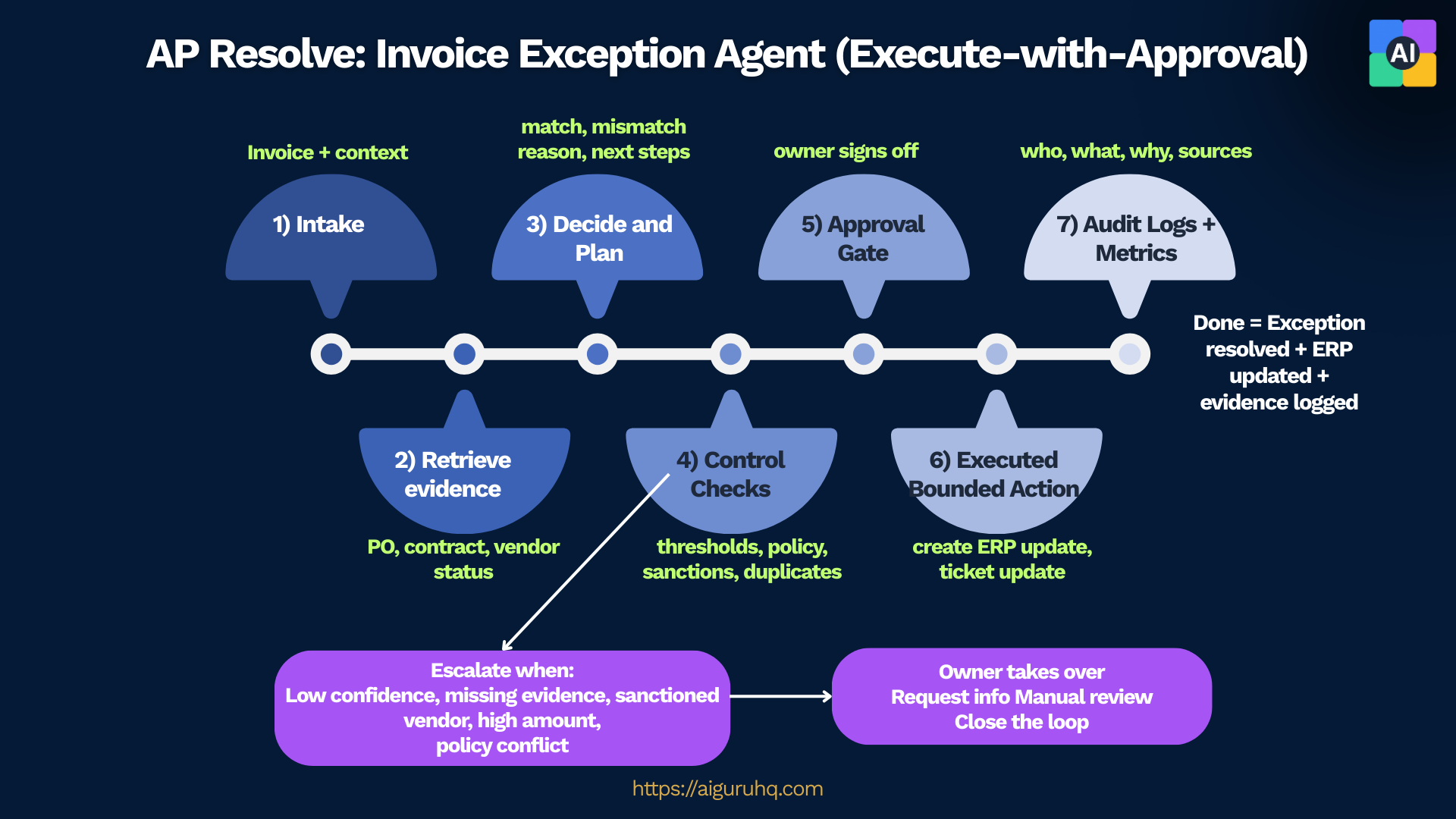
"Agentic" means it can take a real action in a business process, not just generate text. The agent retrieves evidence from systems of record, validates against policies, proposes specific bounded actions, and upon approval, executes those actions with full traceability.
This demo uses bounded autonomy: the agent proposes actions based on evidence and rules, then executes only after human approval. The unit of value is workflow completion (case resolved), not chat responses.
The foundational patterns that make this agent safe and effective
Success is measured by cases resolved, not chat responses. The agent completes real work.
Agent proposes, human decides. No unilateral action on sensitive operations.
All claims cite sources. Every finding links back to POs, contracts, or policies.
Structured audit log with hash chain captures every action, decision, and state change.
Clear escalation for edge cases. Emergency stop mechanism for immediate halt.
The explicit logic that governs agent behavior - no black boxes
These conditions always escalate to human review - no approval option
Agent confidence starts at 90% and adjusts based on evidence
Risk level determines review requirements and escalation paths
Every invoice runs through these checks with evidence citations
A checklist students can map to what they see
Agent can only execute pre-defined bounded actions, never arbitrary operations
Human approval required before any write operation executes
SHA256 hash-chained event log captures every action with who, what, when, why
Automatic escalation for sanctions, vendor mismatch, low confidence; kill switch for emergencies
POs, contracts, and policies retrieved with citations
Sanctions violations, vendor mismatches, low confidence triggers
Every state change, retrieval, decision with hash chain verification
Case resolved, ERP updated, evidence logged, audit complete